Challenge
The relationship between sensitive data and users can be complex, making it difficult to protect against inadvertent or deliberate insider data breaches. ISE neatly circumvents this, as its ontology-based system uses sets of predefined concepts for real- time classification of structured and unstructured data.
- High time to implement
- Requires manual intervention
Augmenter Solution
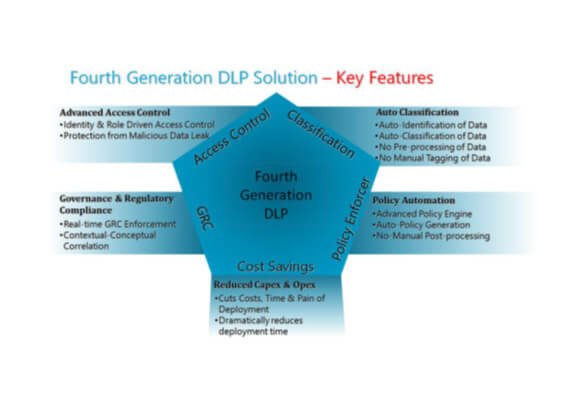
Fourth Generation DLP solutions obviate the critical issues of the previous generations as well as address the challenge of ‘Malicious Data Leak’ scenarios. The Fourth Generation DLP solutions do not depend on manual processes and hence, are non-susceptible to human errors and invulnerable to purposeful acts of ‘Malicious Data Leak’.
The key differentiating characteristics of Fourth Generation DLP solutions are the ability to automate the functions of data/information identification, classification, analysis and enforcement. The Fourth Generation DLP solutions must deliver;
Benefits of DLP
Advanced Access Control
Identify & Role Driven access control, Protection from meticulous data leakage
Auto classification of Data
No Manual Tagging, Auto Identification of Data, Auto classification of Data, No Pre-Processing of Data.
Policy Enforcer
Advanced Policy engine, Auto Policy generation, No Manual Post Processing
Cost Savings
Cuts cost, Time and Pain of deployment, Dramatically reduces deployment time.
Governance & Regulatory Compliance
Real time GRC enforcement, Contextual-Conceptual correlation



